How Routing Attacks Impact Lightning Network Security
The Lightning Network, Bitcoin‘s Layer 2 solution, enables fast, low-cost transactions. However, its reliance on intermediate nodes for routing payments creates vulnerabilities. Routing attacks can disrupt payments, lock funds, and compromise user privacy. These threats not only affect individual transactions but also undermine the network’s reliability and trust.
Key risks include:
- Payment Censorship: Malicious nodes block or delay transactions, causing failures and extra fees.
- Channel Jamming: Attackers lock up liquidity by stalling payments, making channels unusable.
- Privacy Breaches: Techniques like traffic analysis and balance probing expose user data.
Defense strategies include protocol updates like encrypted routing and randomized paths, wallet-level protections like multi-path payments, and tools like BitVault‘s secure routing and threat detection features. Strengthening these measures is essential for maintaining the Lightning Network’s usability and security.
Common Routing Attack Types and Their Effects
Payment Censorship Attacks
Payment censorship attacks occur when malicious nodes intentionally block or drop specific payment packets as they move through the Lightning Network. Unlike random network issues, these attacks are calculated and targeted, posing a serious threat to the network’s reliability.
This type of attack takes advantage of the network’s layered encryption. Malicious nodes can simply refuse to forward payments they want to block, creating deliberate disruptions.
Attackers might choose their targets based on transaction size, timing patterns, or suspected user identities. For instance, they could block all payments over a certain amount, frustrating users attempting larger transactions. Alternatively, they might disrupt payments during peak hours to cause maximum inconvenience.
The financial consequences can be severe. When a payment is censored, users often lose the routing fees already paid to reach the malicious node. If the payment fails and retries are triggered, users may be charged multiple times for the same transaction attempt.
From a broader perspective, censorship attacks weaken the network’s dependability. As payment failures increase, users may lose trust in the Lightning Network’s ability to process transactions smoothly. This erosion of confidence could deter users from adopting the Lightning Network, slowing the growth of Bitcoin’s Layer 2 ecosystem.
Next, let’s explore how attackers disrupt liquidity through channel jamming.
Network Jamming and Denial-of-Service Attacks
Network jamming attacks are a major threat to the Lightning Network’s functionality. In these attacks, malicious actors flood payment channels with stalled transactions, preventing legitimate payments from going through.
One common method is channel jamming, where attackers initiate payments but never complete them. In the Lightning Network, every pending payment locks up Bitcoin as collateral until the transaction is resolved. By abandoning multiple payments, attackers can effectively tie up liquidity across the network.
A single attacker with minimal resources can disrupt hundreds of payment channels at once. This is especially damaging when high-traffic routing hubs are targeted, as these hubs handle a significant portion of the network’s transactions.
Another tactic, slot jamming, exploits the limited number of concurrent payments that a channel can process. Lightning Network channels typically allow only a few dozen simultaneous payments. By filling these slots with stalled transactions, attackers can completely block new payments from being processed.
The economic fallout from jamming attacks is widespread. Businesses relying on Lightning payments may lose revenue during the attack, while individual users face delays in accessing their funds. Node operators also suffer, as their channels become unusable despite having sufficient Bitcoin liquidity.
Now, let’s examine how attackers exploit routing data to compromise user privacy.
Privacy Attacks Through Routing Data
Privacy attacks target the anonymity that draws many users to the Lightning Network. While the network offers better privacy than Bitcoin’s public blockchain, determined attackers can still extract sensitive information about payment flows and user behavior.
One of the most advanced methods is traffic analysis attacks, where malicious nodes observe the timing, amounts, and directions of payments passing through their channels. By correlating this data, attackers can uncover user identities and spending patterns.
The threat becomes even greater when attackers control multiple nodes along common routing paths. This gives them visibility into different segments of the same transaction, enabling them to trace payments from sender to recipient.
Another tactic, balance probing attacks, involves sending fake payments to determine channel balances. By testing payments of varying amounts and noting which ones fail, attackers can estimate how much Bitcoin is stored in specific channels. This information can be used to identify high-value users or predict future payment activity.
The consequences of these privacy breaches go beyond individual transactions. Attackers can create detailed profiles of user behavior, including spending habits, business relationships, and financial patterns. For users who rely on Lightning to avoid the transparency of Bitcoin’s blockchain, these breaches represent a serious violation of their expectations.
What makes privacy attacks particularly troubling is their stealthy nature. Unlike payment failures or network disruptions, users are often unaware that their privacy has been compromised. This lack of visibility makes it difficult to detect and measure the full extent of these attacks, leaving the broader Lightning Network community vulnerable.
Clara Shikhelman: Unjamming Lightning
How Routing Attacks Affect Lightning Network Security
Routing attacks create ripple effects that weaken the Lightning Network’s security and performance. They don’t just interfere with individual transactions – they also jeopardize the network’s overall reliability as a payment system. Here’s how these attacks impact payment integrity, fund access, and user privacy.
Payment Failures and Network Reliability Issues
When routing attacks succeed, they often trigger a chain reaction of failures, making payments less reliable and predictable. For users – especially merchants who rely on quick, seamless transactions – this can mean repeated disruptions. Malicious nodes that block or delay payments force the network’s routing algorithms to choose longer and less efficient paths, further straining the system.
Fund Lockups and Financial Risks
Routing attacks like channel jamming and replacement cycling attacks can lock up funds temporarily or even for extended periods[1][2]. In a channel jamming attack, attackers intentionally clog payment channels with stalled transactions, tying up the funds that act as collateral. Replacement cycling attacks, on the other hand, can lead to direct financial losses. These disruptions don’t just halt transactions; they also prevent users from accessing their funds for other purposes, leading to missed opportunities. These financial risks add to the challenges already faced by users.
User Privacy Risks and Data Exposure
Privacy is another major casualty of routing attacks. Techniques like balance probing can expose sensitive transaction details. The concept of Interdependent Privacy (IDP) is particularly relevant here: in multi-hop payments, intermediary nodes gain access to information about payment amounts and timing, leaving users with limited control over their data[3]. Adversaries can use route correlation or man-in-the-middle attacks to trace payments, further eroding privacy[1]. Even though onion routing encrypts much of the routing data, payment amounts remain visible to all nodes along the path[3][4].
For individuals who rely on Bitcoin’s pseudonymity – such as journalists, activists, or those living under authoritarian regimes – these privacy risks can pose serious threats to their safety and freedom[1][3]. The mere possibility of transaction monitoring might discourage these groups from using the Lightning Network altogether. These risks highlight the urgent need for stronger protective measures to ensure the network remains secure and trustworthy.
sbb-itb-c977069
Defense Strategies Against Routing Attacks
The Lightning Network community has implemented a variety of strategies to counter routing attacks and bolster network security. These measures range from protocol-level improvements to wallet-specific protections, creating a comprehensive defense system against malicious activities.
Protocol-Level Security Measures
Protocol-level defenses focus on network-wide adjustments to address vulnerabilities and enhance privacy.
One such measure is cover traffic, where nodes generate fake transactions to obscure real payment patterns. This technique complicates balance probing and timing analysis attacks. Similarly, constant-size messages ensure all routing communications are uniform, preventing attackers from using message size as a clue.
Advanced cryptographic tools like Point Time-Locked Contracts (PTLCs) and Taproot channels also play a key role. PTLCs replace traditional hash preimages with digital signatures, making it impossible for intermediary nodes to link payments across channels. Taproot channels, on the other hand, improve privacy by making multi-signature transactions indistinguishable from single-signature ones on the blockchain.
The use of onion messaging adds another layer of security. By encrypting routing data in multiple layers – similar to how Tor works – each node only sees the information necessary for its role. This ensures no single node can access the complete payment path, safeguarding user privacy.
Random Path Selection and Fee Strategies
Predictable routing algorithms can make the network vulnerable to attacks. To counter this, randomized path selection introduces controlled unpredictability, making it harder for attackers to anticipate or manipulate payment routes.
Another tactic is fee randomization, which slightly varies routing fees to obscure payment patterns. Instead of always opting for the cheapest route, wallets may occasionally select slightly more expensive paths to enhance privacy and reduce the likelihood of attacks.
Multi-path payments split larger transactions into smaller pieces that travel through different routes simultaneously. This not only increases the chances of payment success but also makes it significantly harder for attackers to monitor or block the entire transaction.
Additionally, some wallets use decoy routing, where fake payment attempts are generated alongside real ones. These decoy payments drain attacker resources and create noise, making it more difficult to distinguish genuine transactions from the false ones. This strategy works similarly to cover traffic but operates at the individual wallet level.
How Non-Custodial Wallets Like BitVault Help
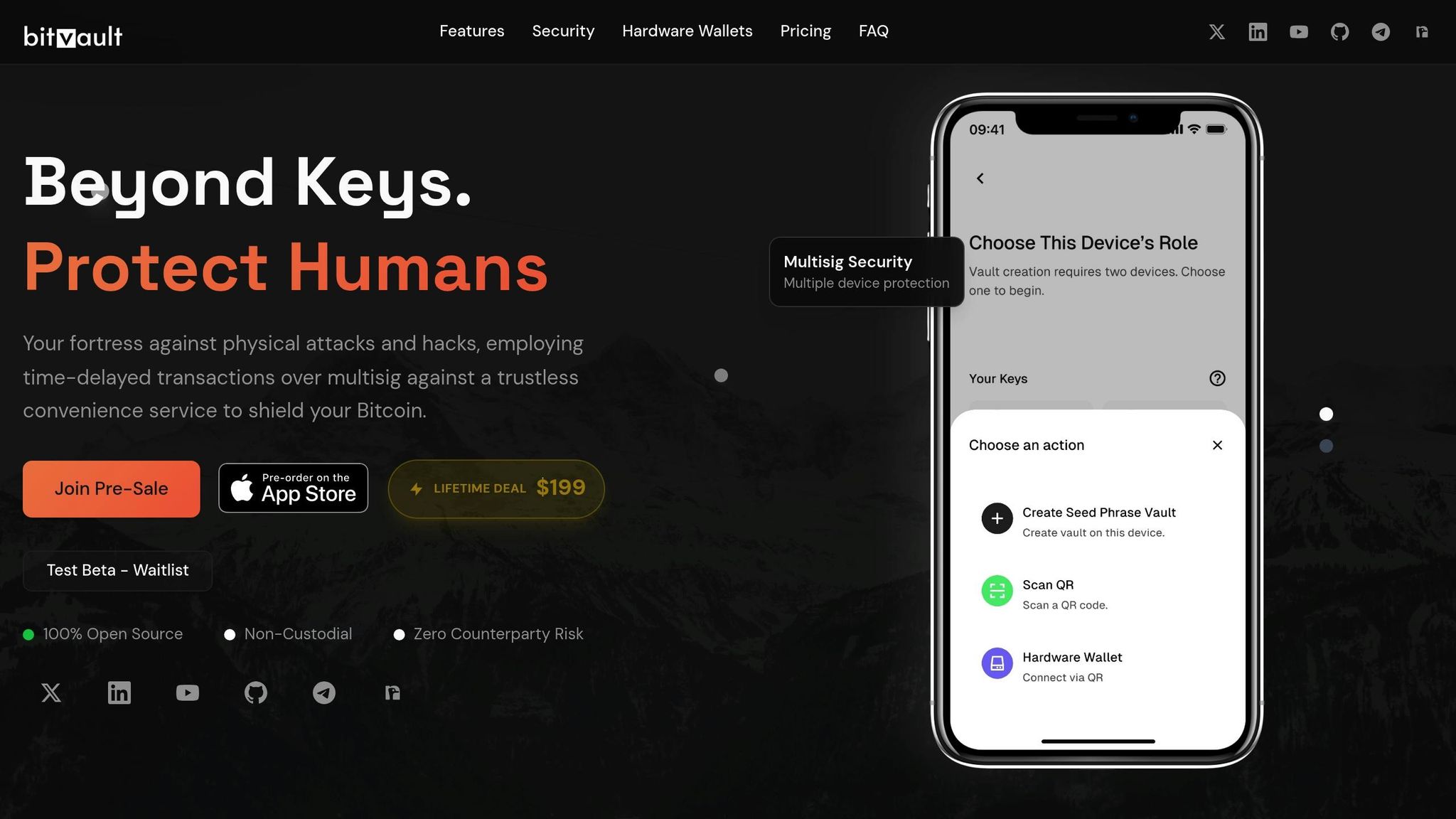
Non-custodial wallets, such as BitVault, provide users with additional safeguards against routing attacks, particularly those targeting transaction timing or channel closures. For instance, time-delayed transactions give users extra time to detect and respond to suspicious activity, reducing the risk of replacement cycling attacks.
BitVault also employs multisig convenience services, which mitigate the financial impact of channel jamming attacks. If funds are tied up in Lightning channels, users can still access their Bitcoin through alternative multisig pathways, ensuring continuity and security.
With its integration of both Liquid and Lightning Networks, BitVault offers users flexible routing options. In the event of widespread attacks on the Lightning Network, users can seamlessly switch to Liquid Network transactions, maintaining access to their funds without compromising security.
The wallet’s secret notification system is another critical feature. It alerts users to unusual activity that may indicate routing attacks, helping them decide whether to proceed with Lightning payments or opt for more secure alternatives based on current network conditions.
Lastly, AES 256-bit encryption safeguards wallet data and transaction details, protecting users from attackers attempting to correlate on-chain activity with Lightning payments. This encryption ensures that even if some transaction metadata is exposed, the most sensitive information remains secure. By addressing privacy concerns and minimizing the risk of fund lockups, BitVault strengthens the overall resilience of the Lightning Network.
Key Takeaways on Lightning Network Routing Security
The Lightning Network faces significant risks from routing attacks. By understanding these threats and adopting effective defenses, users and developers can work toward creating a safer payment environment.
Main Routing Attack Risks
Routing attacks pose serious challenges for Lightning Network users and the ecosystem as a whole. One major threat is payment censorship attacks, where malicious nodes block or redirect transactions. This can prevent users from accessing their funds or completing urgent payments.
Another concern is network jamming and denial-of-service attacks. These attacks can tie up liquidity, forcing users to pay higher fees. When attackers lock up capital for extended periods, legitimate users may struggle to route their payments effectively.
Privacy attacks are also a growing issue. Malicious nodes can analyze routing data to uncover payment patterns, probe channel balances, and link transactions. This can lead to the creation of detailed user profiles, exposing spending habits. Such data may be exploited for targeted attacks or sold to third parties, undermining the privacy that cryptocurrency users often seek.
These risks highlight the importance of implementing strong security measures to protect the network.
Why Defense Measures Are Critical
To address these vulnerabilities, robust defense strategies are essential for the Lightning Network’s continued growth and reliability.
At the protocol level, improvements like enhanced onion routing and Point Time-Locked Contracts (PTLCs) are critical. These technologies obscure payment paths and prevent intermediary nodes from linking transactions, making it harder for attackers to exploit routing data.
On the user side, wallet-level protections are equally vital, especially when network-wide defenses fall short. For example, BitVault (https://bitvault.sv), a non-custodial Bitcoin wallet, demonstrates how advanced wallet features can enhance security. By offering secure multi-network routing and real-time threat detection, BitVault gives users more control over their transaction safety. Its open-source design further ensures transparency and trust.
The Future of Lightning Network Security
The security of the Lightning Network will continue to evolve through collaboration between protocol developers, wallet creators, and the broader Bitcoin community. Advances in cryptography and routing algorithms will make attacks more complex and expensive to execute.
Wallet innovation will be a key driver in this evolution. Features like multi-network integration, smarter routing options, and real-time threat detection are likely to become standard, providing users with greater flexibility and protection. As these technologies mature, the adoption of standardized security practices across platforms and node implementations will further strengthen the network, ensuring safer Lightning payments for everyone.
FAQs
What are routing attacks on the Lightning Network, and how do they impact transactions?
Routing attacks on the Lightning Network take advantage of weaknesses in how payments are routed between nodes. Two common examples are time-dilation attacks, where attackers deliberately slow down transactions to cause disruptions or potentially steal funds, and mass exit attacks, which flood the network with activity, leading to payment failures and instability.
The consequences of these attacks can be severe, including delayed or failed transactions, a drop in network reliability, and even the risk of losing funds. To counter these threats, strategies such as diversified routing, watchtowers, payment splitting, and anti-eclipse measures are employed. These methods aim to boost the network’s resilience and safeguard user assets.
How can privacy attacks on the Lightning Network expose user identities, and what steps can be taken to protect anonymity?
Privacy concerns on the Lightning Network, like route correlation and transaction analysis, pose a real risk. These methods can potentially reveal user identities by mapping payment routes and estimating transaction specifics, threatening the anonymity users count on.
To tackle these issues, the Lightning Network uses onion routing, a method that hides transaction paths by encrypting data in multiple layers. Users can further protect their privacy by leveraging tools like Tor, which helps obscure network activity. Other strategies, such as splitting payments into smaller chunks or regularly changing transaction routes, add extra layers of complexity, making it much harder for attackers to track and expose payments. When combined, these techniques offer a robust way to guard against privacy breaches on the Lightning Network.
What are the best ways to defend against routing attacks on the Lightning Network, and how do they enhance security?
To protect against routing attacks on the Lightning Network, users can take several practical steps. One key approach is route diversification, which involves spreading transactions across multiple paths to reduce the risk of interference. Pairing this with connections to trusted nodes adds another layer of security, making it harder for attackers to exploit vulnerabilities.
Keeping an eye on network activity is equally important. By analyzing unusual patterns, users can spot and address potential threats early. Partnering with well-regarded and reliable nodes also strengthens the network’s defenses. These actions not only safeguard user funds but also boost the reliability and trustworthiness of the Lightning Network as a whole.