Checklist for Multi-Signature Governance Setup
Multi-signature governance is a way to secure Bitcoin by requiring multiple digital signatures to approve transactions. Instead of relying on a single private key, this method spreads control across multiple keys, reducing risks like theft, coercion, and errors. For example, a 2-of-3 setup allows access with any two of three keys, ensuring both security and flexibility.
Key Steps for Setting Up Multisig Governance:
- Define Roles: Assign responsibilities for managing keys, approving transactions, and handling emergencies.
- Set Policies: Choose an M-of-N configuration (e.g., 2-of-3) based on security needs.
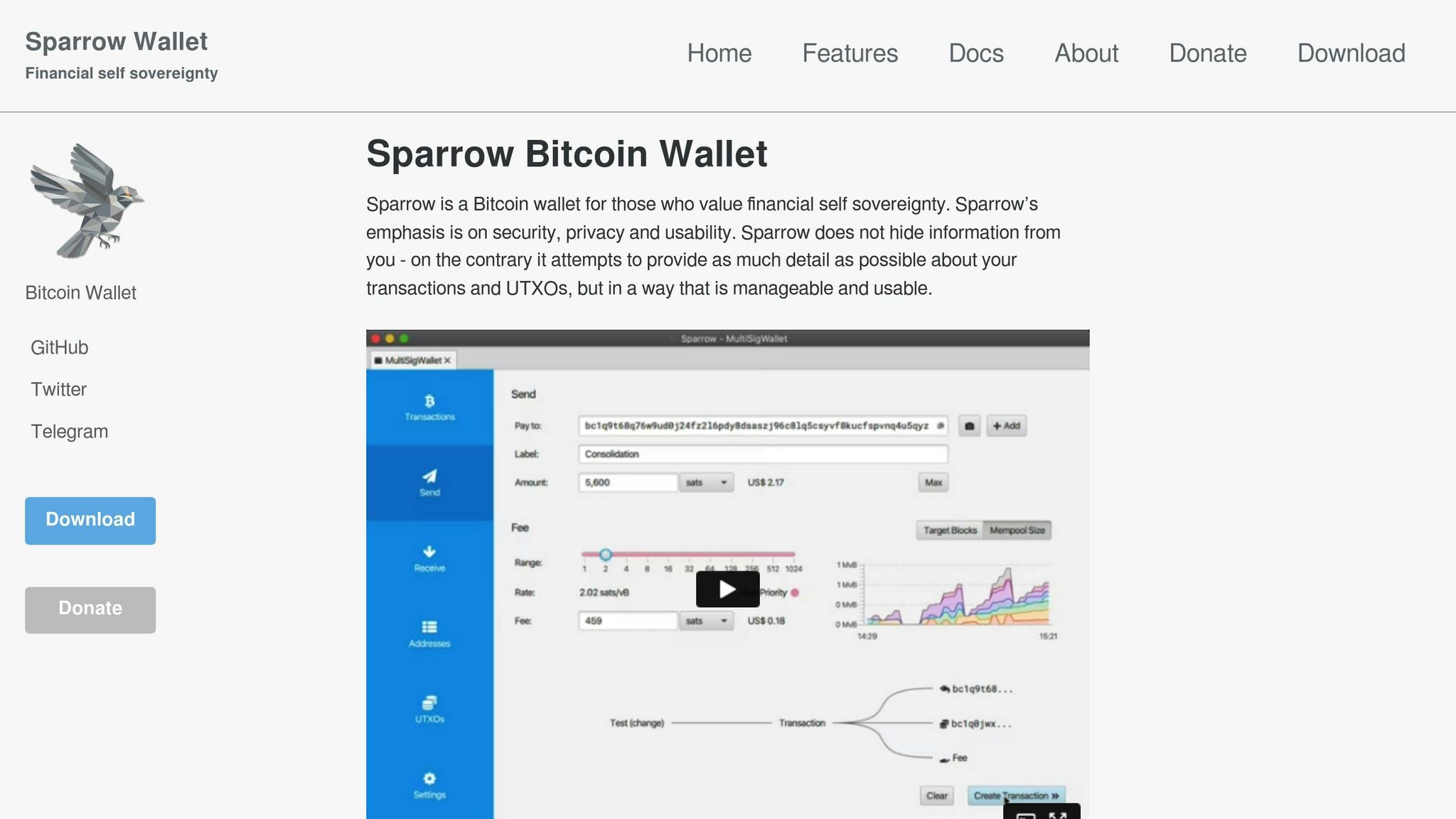
- Choose a Wallet: Use a reliable platform like BitVault, which supports hardware wallets and advanced features like time-delayed transactions.
- Generate Keys Securely: Create keys offline with hardware wallets and store them in tamper-proof locations.
- Test & Document: Run test transactions, document procedures, and ensure all stakeholders know their roles.
- Backup & Recovery: Store backups in multiple locations and plan for key loss or transitions.
Using tools like BitVault ensures added layers of protection, such as time delays and encrypted alerts, while regular audits and updates help maintain long-term security. By adopting these practices, you can confidently manage your Bitcoin with reduced risks and increased control.
Sparrow Wallet Multisig | The Most Secure Bitcoin Wallet Set Up 🔐
Prerequisites for Multi-Signature Governance Setup
Before diving into the technical details of setting up multi-signature governance, it’s crucial to establish a strong governance framework. This step ensures your Bitcoin management strategy is secure and operates efficiently. Here’s how to get started on the right foot.
Identify Stakeholders and Define Roles
Start by pinpointing the key stakeholders who will be involved in your multisig governance. Assign clear roles and responsibilities for tasks like managing private keys, approving transactions, and handling recovery protocols. Decide who will hold the keys, how transactions will be verified, and what procedures are in place for emergencies. It’s also a good idea to ensure participants have the necessary technical skills and to consider geographic diversity. This reduces the risks associated with localized disruptions.
Set Signing Policies and Thresholds
Determine a signing policy that strikes the right balance between security and usability. In multisignature setups, this often involves selecting an M-of-N configuration – where "M" is the minimum number of signatures required out of "N" total keys. Tailor this setup to fit your risk tolerance and operational needs. For instance, you might want stricter approval thresholds for larger transactions or implement emergency protocols for quick decision-making when needed.
Address Legal and Compliance Considerations
Take the time to understand the legal and regulatory requirements that apply to your setup. Document all key processes thoroughly, and consult with a cryptocurrency attorney to ensure you’re staying compliant with relevant laws. Once these foundational steps are in place, you’ll be ready to move forward with configuring your multisig governance system.
Step-by-Step Checklist for Multisig Governance Setup
Select a Multisig Wallet Platform
Start by choosing a reliable multisig wallet platform. BitVault is a strong option – it’s open-source, non-custodial, and compatible with hardware wallets like Jade Plus. It also includes features like time-delayed transactions and secret notifications.
Because it’s open-source, your technical team can audit the code to ensure it meets your security standards. Plus, BitVault works smoothly with various devices, making it a flexible choice.
When reviewing platforms, look for those that support Miniscript technology. This feature allows for more adaptable security policies, which can be especially useful as your governance needs grow and change over time.
Generate and Distribute Keys Securely
Once you’ve selected a platform, the next step is to focus on secure key generation. Always generate seed phrases offline using dedicated hardware wallets. Avoid creating them on devices connected to the internet or shared systems.
When distributing extended public keys (xpubs), use encrypted communication channels and verify each xpub through multiple methods to guard against man-in-the-middle attacks. It’s also important to document which hardware wallet generated each key and clearly assign ownership to specific individuals.
For added security, store seed phrases in geographically dispersed locations using tamper-proof storage solutions. Each key holder should have clear, step-by-step instructions for accessing their seed phrase in case of an emergency.
Configure the Multisig Wallet
Set up your wallet using the pre-determined M-of-N configuration. Import the xpubs, set the signing threshold, and establish governance rules, such as approval workflows, spending limits, and notification settings.
To boost security, implement time-locked contracts within your governance rules. For instance, you can set mandatory waiting periods for high-value transactions or automate approvals for routine operations.
Leverage BitVault’s secret notification system to keep stakeholders informed about pending transactions. This system alerts designated parties without exposing sensitive details, striking a balance between security and transparency.
Test and Document the Setup
Before fully deploying the wallet, run small test transactions to confirm that thresholds and emergency workflows function as expected.
Create detailed documentation outlining key storage locations, stakeholder responsibilities, backup procedures, and recovery instructions. Include contact details for all key holders and establish clear communication protocols for various scenarios. Store this documentation securely but ensure it’s accessible to authorized personnel when needed.
Test all threshold signatures to ensure they work as intended. For example, verify that transactions are successfully approved when the minimum number of signers participate and that they fail appropriately when there aren’t enough signatures.
Set Up Backup and Recovery Processes
After confirming the setup works as intended, focus on building a robust backup and recovery plan. Store seed phrases and wallet configurations (xpubs, derivation paths, and other settings) in tamper-proof storage across multiple locations. Schedule regular recovery drills to ensure the process runs smoothly.
Plan for key holder transitions, whether due to personnel changes or emergencies. Your strategy should include clear steps for onboarding new signers and safely removing departing ones from the configuration.
You might also want to incorporate BitVault’s time-delayed transaction feature into your recovery plan. These delays provide a critical window to detect unauthorized access and, if necessary, cancel suspicious transactions before they’re executed.
sbb-itb-7e890ce
Security Best Practices for Multisig Governance
Use Hardware Wallets for Key Management
When it comes to safeguarding your private keys, hardware wallets are your best friend. These devices keep your keys completely offline, isolating them from potential online threats. By storing keys in secure chips, hardware wallets protect against both digital hacks and physical tampering. With BitVault’s integration of hardware wallet support, you can add an extra layer of security to your multisig governance setup.
Implement Time-Delayed Transactions and Alerts
Once your keys are secured offline, it’s smart to add another layer of protection by using time-delayed transactions. These delays act as a safety net, enforcing a waiting period before a transaction gets broadcast to the Bitcoin network. BitVault’s time-locked contracts ensure funds can’t be accessed immediately, which is especially useful in situations where coercion might be a risk.
To complement this, BitVault offers an encrypted alert system that notifies designated devices when a transaction is initiated. This system keeps stakeholders informed without revealing sensitive details. For even better protection, you can customize delay periods based on the transaction’s size or associated risks, tailoring your approach to meet specific security needs.
Maintenance and Governance Management
Conduct Regular Audits and Reviews
It’s essential to routinely audit your multisig setup to ensure security measures are up to date and policies align with your team’s needs. These audits should confirm that all authorized signers still have access to their keys and that any former team members no longer retain signing privileges. Additionally, it’s wise to reassess signing thresholds regularly to make sure they still fit the team’s evolving requirements.
Take this opportunity to review governance policies, such as spending limits and approval workflows, to ensure they remain appropriate. Backup and recovery strategies, like seed phrase backups, should also be tested periodically to verify their effectiveness. Documenting audit results and any adjustments made is crucial – these records can serve as a reference point for compliance purposes or during transitions within the team.
Regular audits also pave the way for effective succession planning.
Plan for Key Loss and Succession
Unexpected situations, like the loss of a key or a signer becoming unavailable, can disrupt operations. To address this, establish clear succession protocols that outline the steps to take in these scenarios. These protocols should detail how signing responsibilities will be transferred and ensure the process is smooth and well-documented.
To add redundancy to your governance structure, designate backup signers and make sure everyone involved understands the procedures. Communication protocols are equally important – relevant parties need to know how to respond if a key becomes inaccessible. Simulate scenarios periodically to test your succession plans and identify any weak points that need improvement.
While safeguarding the human element, don’t overlook the importance of keeping your software secure and updated.
Monitor Software Updates and Security Patches
Staying on top of software updates and security patches is a critical part of maintaining a secure multisig wallet. Regularly test and apply updates to ensure your setup remains protected without causing disruptions.
Before rolling out updates in your live environment, test them thoroughly to confirm compatibility with your workflows and hardware. Coordinate update schedules among all signers to avoid compatibility issues across devices.
Keep a record of software versions, update dates, and any issues that arise during the process. This documentation not only simplifies troubleshooting but also helps ensure your security policies are consistently followed.
Key Takeaways for Multisig Governance
Creating a secure multisig governance system requires well-defined roles for stakeholders, strict signing policies, and thresholds that strike a balance between security and operational ease.
Here’s a quick breakdown of the essentials: Hardware wallets are a must for managing keys offline, offering a solid defense against cyber threats. Pairing this with time-delayed transactions adds another layer of protection, giving you crucial time to respond to potential threats – whether they’re digital attacks or physical coercion.
Modern tools like Miniscript and threshold signatures can elevate your security game. These tools allow for more advanced governance setups, going beyond the basic multisig configurations and adapting to future needs.
Every step of the process – key generation, recovery, and beyond – should be documented and tested regularly. This includes running through emergency scenarios, validating backup systems, and ensuring that every team member knows their responsibilities inside and out.
By adopting multi-signature self-custody, you take control of your Bitcoin, moving away from reliance on exchanges. While this offers true ownership, it also comes with the responsibility of maintaining top-notch security. Regular audits, along with keeping your software up to date, are critical to sustaining a strong governance framework.
Think of your multisig governance as a dynamic system. To ensure its long-term effectiveness, conduct regular audits, plan for team changes, and stay ahead of evolving threats. Investing time and effort into a solid setup and ongoing maintenance not only strengthens security but also gives you peace of mind when it comes to safeguarding your Bitcoin.
FAQs
What are the main advantages of using a multi-signature setup for securing Bitcoin over a single private key?
A multi-signature (multisig) setup adds an extra layer of security to Bitcoin transactions by requiring multiple keys to approve a transaction. This approach minimizes the risk of losing funds due to a single point of failure, such as a lost or stolen private key.
By spreading control across several keys, multisig wallets help safeguard against theft, accidental key loss, or unauthorized access. They’re especially valuable for situations involving shared decision-making or for securing substantial amounts of Bitcoin, providing both added protection and reassurance.
What steps should I take to securely generate and distribute keys in a multi-signature Bitcoin setup?
To ensure secure key generation and distribution in a multi-signature Bitcoin setup, start with trusted hardware wallets or secure offline devices for creating the keys. Spread the keys across different locations, making sure no single person or organization has access to all of them. For added safety, keep backups in secure, geographically separated places like safe deposit boxes or fireproof safes to guard against physical loss or damage. Stick to encryption best practices and avoid sharing sensitive details online to reduce the chances of unauthorized access.
How can I regularly maintain and audit my multi-signature governance system to ensure it stays secure and compliant?
To keep your multi-signature governance system running smoothly and securely, here are some essential practices to follow:
- Review key holders regularly: Double-check that everyone with access is still authorized and capable of carrying out their responsibilities. If there are team changes, make sure access is updated promptly.
- Test recovery plans: Run through scenarios like lost keys or hardware failures every so often. This ensures your backup and recovery systems are reliable and ready when needed.
- Keep an eye on transaction logs: Regularly check transaction activity for anything out of the ordinary. If you spot something suspicious, investigate and resolve it immediately.
- Maintain hardware security: Update firmware on all hardware wallets and devices in use, and ensure they’re stored securely to prevent tampering or theft.
Staying on top of these tasks helps minimize risks and keeps your governance system strong and dependable.
Related Blog Posts
- How to Set Up a Bitcoin Multisig Wallet
- Bitcoin Treasury Compliance vs. Risk
- Multisig Wallets: Reducing Mnemonic Risks
- Internal Controls for Bitcoin Custody
https://app.seobotai.com/banner/banner.js?id=691e843b9c1061ed16168dc1