From Mnemonic to Address: What Really Happens Under the Hood
By mordom
Anyone who owns Bitcoin is familiar with the 12 or 24 words.
We call them a “seed phrase”.
But they are not the seed.
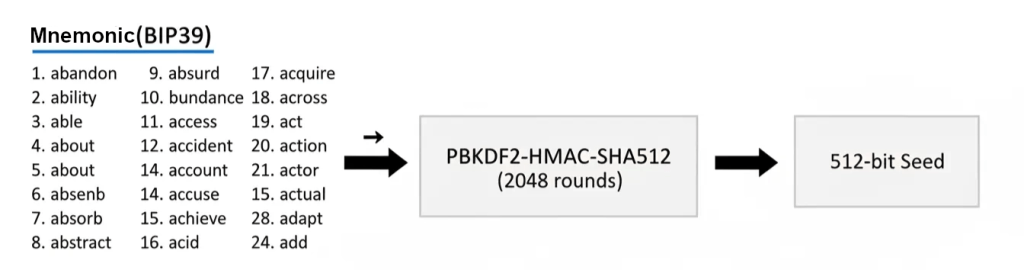
And this is where one of the most common misunderstandings begins: many people confuse the mnemonic (BIP39) with the actual cryptographic seed.
The words are a human-readable representation of the original entropy.
The seed, instead, is a 512-bit binary value derived afterward through a cryptographic function.
The words are the human input.
The seed is the mathematical output.
Understanding this distinction changes the entire perspective.
1. From Words to Seed: What PBKDF2 Actually Does
The mnemonic is not used directly to generate keys. First, it is processed through a function called PBKDF2-HMAC-SHA512.
It’s important to be precise about the parameters:
- Password → the mnemonic (the 12 or 24 words)
- Salt → the string “mnemonic” concatenated with the passphrase
So the salt is: “mnemonic” + passphrase.
If no passphrase is set, it is simply an empty string. It is not zero — it is an empty string (length = 0).
The function runs 2048 iterations, slowing down potential brute-force attacks.
The result is a 512-bit binary value. That is the actual seed.
A single different character in the passphrase produces a completely different seed. There are no partial overlaps.
2. From Seed to Hierarchical Structure: BIP32
The seed is then processed according to BIP32, which defines hierarchical deterministic wallets (HD wallets).
An HMAC-SHA512 is computed using the key “Bitcoin seed”, producing a 512-bit output and split into two parts:
- IL → becomes the master private key
- IR → becomes the master chain code
The root key is therefore not just a private key, but a pair composed of:
- private key
- chain code
From this pair, the entire tree structure emerges.

Every time a child key is generated, the derivation function uses:
- the parent node’s key
- the parent node’s chain code
The output is a new pair: child key and new chain code.
The chain code is what makes hierarchical derivation possible while preserving both security and determinism. Without it, secure HD wallets would not exist.
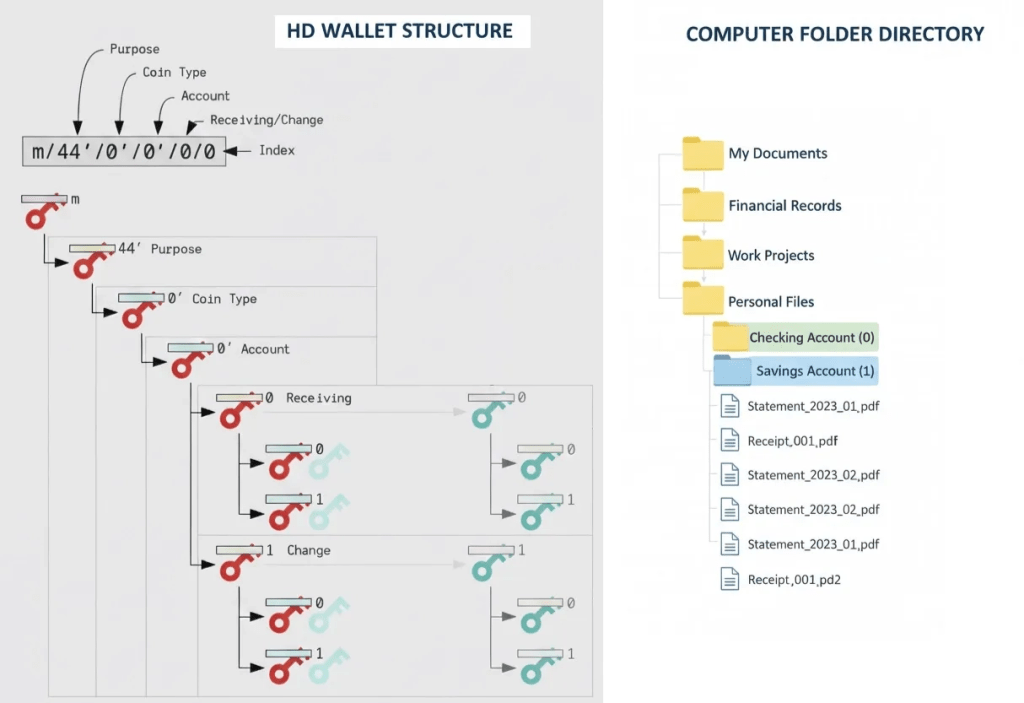
3. The Key Tree and the Derivation Path
Starting from the root key, BIP32 allows the creation of a potentially infinite tree of keys.
A typical path may look like:
m / 84’ / 0’ / 0’ / 0 / 0
Each level has a specific meaning:
- m → master key
- 84’ → standard (BIP84, native SegWit)
- 0’ → coin type (Bitcoin mainnet)
- 0’ → account
- 0 → external chain (receiving addresses) – 1 for change
- 0 → address index
Each level represents a new application of the derivation function.
When a wallet generates a new address, it is not creating randomness.
It is simply incrementing an index along a branch that was already mathematically determined by the original seed.
All future addresses are already implicit in that initial entropy.
4. What a Wallet Actually Stores
A wallet can manage different levels of the hierarchy:
- master private key
- account keys
- extended public keys (xpub, zpub, etc.)
An extended public key contains:
- public key
- chain code
This allows the generation of all addresses within a branch without knowing any private keys.
That’s why:
- a watch-only wallet can display addresses
- sharing an xpub does not allow spending, but it does reveal the transaction structure
This distinction is the foundation of multisig setups, air-gapped configurations, and advanced custody models.
5. Why Some Addresses Start with “1”, Others with “3” or “bc1”
The difference does not originate from the seed.
It originates from the standard used in the derivation path.
In short:
- BIP44 → legacy addresses
- BIP49 → nested SegWit
- BIP84 → native SegWit
Same seed, same underlying mathematical structure.
What changes is how the public key is transformed into an address.
6. BIP39 and BIP32: Distinct Roles
It is worth repeating.
BIP39 handles the transformation of entropy into words (and back).
BIP32 defines how a hierarchical key tree is built from a seed.
One concerns human usability.
The other defines the cryptographic structure.
They are complementary — but not interchangeable.
A Different Perspective on Self-Custody
When you write down 24 words on a piece of paper, you are not storing addresses — you are storing entropy in readable form.
From that entropy comes a seed. From the seed, a master key (IL) and its chain code (IR) are generated. From that pair, a deterministic key tree takes shape.
A wallet does not “create” addresses in the common sense.
It simply navigates a mathematical structure that was already defined at the moment the entropy was generated — much like browsing folders on a computer: the files are not created each time, they already exist within the structure.
It’s not magic. It’s organized cryptography.
And understanding this fundamentally changes how one thinks about self-custody.
If understanding how a mnemonic becomes authority changed how you see Bitcoin, it might be time to rethink how that authority is protected and what impacts it has on your self-custody approach. Explore BitVault quietly at your own pace.
Technical Note
For simplicity, we did not explore:
- the distinction between normal and hardened derivation
- the detailed mechanics of index handling in the derivation process
In HD wallets, indices are 32-bit numbers:
- normal derivation → from 0 to 2³¹−1 and allows derivation from public keys
- hardened derivation → from 2³¹ to 2³²−1 and requires the parent private key
Hardened indices are conventionally indicated with an apostrophe in the derivation path (e.g., 84’).