Bitcoin Wallet Entropy: How “Random” Is Really Enough?
By mordom

In the process of creating a Bitcoin wallet, everything depends on a single initial value: entropy. If that entropy is unpredictable, the wallet is secure.
If it’s not, no hardware wallet, multisig, or backup can fix it.
In Bitcoin, a private key is an integer k such that:
1 ≤ k < n (see Technical Note at the end for details)
where n is the order of the secp256k1 elliptic curve.
In theory, this implies a keyspace of approximately 2²⁵⁶ possible values. In practice, security depends on how unpredictable the process that chooses k is.
Everything else — addresses, public keys, seed phrases — is a deterministic mathematical consequence of this initial value.
Entropy and keyspace
When we talk about “128 bits” or “256 bits” of entropy, we’re referring to the size of the possible key space:
- 128 bits → 2¹²⁸ possibilities
- 256 bits → 2²⁵⁶ possibilities
For comparison, even a brute-force attack capable of testing billions of keys per second would remain completely ineffective. Already 128 bits of effective entropy are considered more than sufficient against any practical attack today.
This clarifies a commonly misunderstood point:
the problem is not the size of the keyspace, but the quality of the initial distribution.
A generator that promises 256 bits but produces correlated or predictable values drastically reduces the actual search space.
Theoretical entropy vs effective entropy
In cryptography, it’s essential to distinguish between:
- nominal entropy (what’s declared)
- effective entropy (what’s actually unpredictable)
A system can produce apparently uniform values derived from deterministic processes. If an attacker can model or reconstruct that internal state, security collapses.
Formally, uniformity alone is not sufficient: values must also be statistically independent and free from temporal correlation.
Historically, many security failures were not caused by weak algorithms, but by poorly initialized pseudo-random number generators (PRNGs) or insufficient entropy sources.
In the context of Bitcoin wallets, this means that the cryptographic strength of the elliptic curve is irrelevant if the initial entropy is compromised.
Where wallet entropy comes from
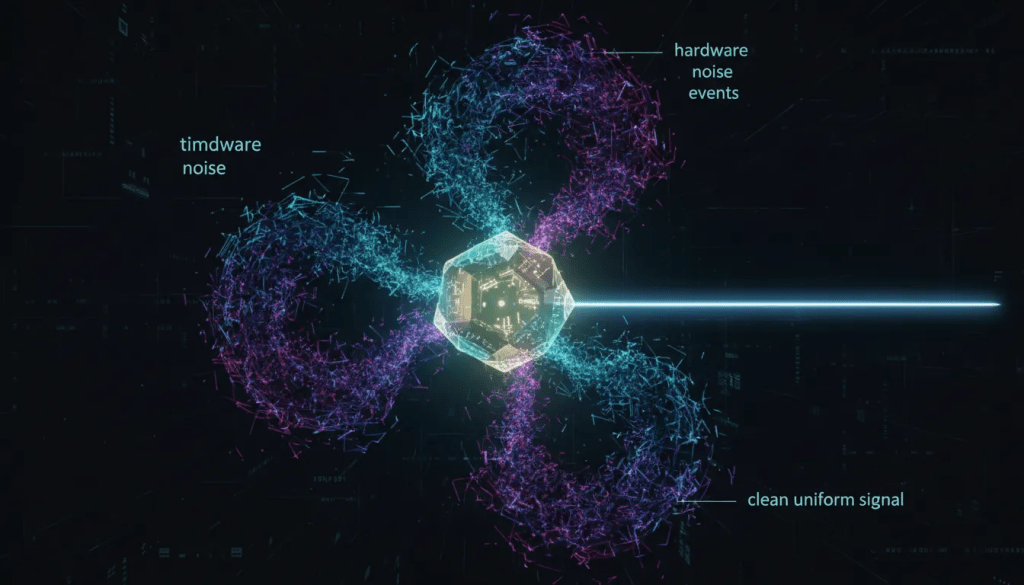
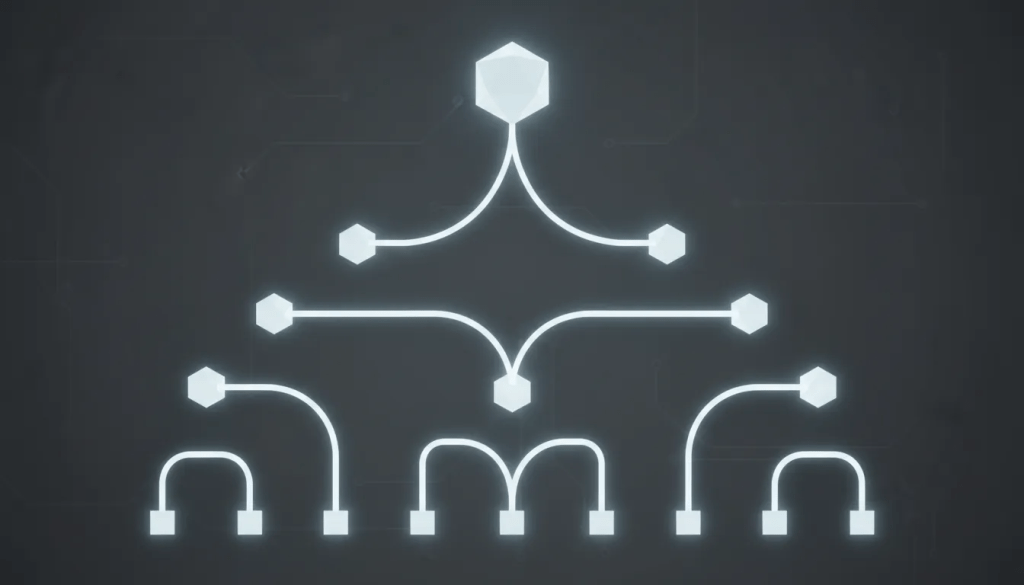
Modern wallets use CSPRNGs (Cryptographically Secure Pseudo-Random Number Generators), initialized from multiple noise sources, including:
- temporal jitter
- hardware noise
- asynchronous system events
- non-deterministic environmental inputs
These sources are combined and “compressed” using cryptographic hash functions — typically SHA-256 — to produce a uniform, unpredictable output.
From the user’s perspective, this process is a black box: it’s neither observable nor verifiable after the fact. Trust therefore shifts to:
- the implementation
- the execution environment
- the quality of the code and libraries used
The entropy problem is not a brute-force attack, but an attack on the generation process, where the attacker drastically reduces the keyspace by modeling or replicating the PRNG.
The link to seed phrases (BIP39)
In BIP39-based wallets, the initial entropy is typically:
- 128 bits (12 words)
- 256 bits (24 words)
A checksum is added to this entropy, and the result is mapped to a list of 2048 words.
It’s important to note that:
- the seed phrase is not the entropy
- it’s just a human-readable representation of it
If two wallets generate the same initial entropy, they will produce the same seed phrase and the same set of keys, regardless of the device or software used.
Why entropy problems are difficult to detect
A wallet with weak entropy:
- functions correctly
- signs valid transactions
- shows no visible anomalies
Unlike a missing backup or forgotten passphrase, an entropy problem produces no warning signals. The user may only discover it when funds are moved by third parties — often long after the wallet was created.
This makes entropy one of the most insidious failure points: critical, invisible, irreversible.
More control ≠ more entropy
A common mistake is thinking that adding manual steps or custom procedures automatically increases security.
From an entropy perspective:
- human error introduces bias
- repeatability reduces unpredictability
- complexity increases the error surface
A theoretically correct process executed imperfectly can produce less real entropy than a well-implemented standard solution.
Control has value only when accompanied by a real understanding of the underlying mechanisms.
What really matters
When evaluating wallet security, the right question isn’t “how many bits does it use?”, but:
- where does the entropy come from?
- how is it combined?
- how robust is the implementation?
- how much has it been analyzed over time?
Modern cryptography is extremely solid. Weaknesses almost always emerge at the edges, in the interaction between theory, implementation, and real-world use.
Conclusion
Entropy is the mathematical root of Bitcoin wallet security.
If it’s unpredictable, everything else works.
If it’s not, nothing can compensate for it.
Understanding this does not require being a cryptographer — only recognizing that security does not emerge from the number of tools used, but from the quality of the very first step.
Because in Bitcoin, before backups, devices, or multisig, there’s only one question that really matters:
How unpredictable is your private key?
Entropy is one of those things you only think about when it’s already too late. At BitVault, we design Bitcoin wallets assuming randomness, keys, and recovery are all stress-tested in the real world — including under pressure and failure scenarios.
If you’re exploring higher-assurance Bitcoin self-custody, you can review BitVault’s early access plans here.
- Technical note In Bitcoin, n is the order of the group generated by the generator point G on the secp256k1 elliptic curve. Each public key is derived as K=k⋅G. After n scalar multiplications, the group “wraps around”, defining the finite set of valid private keys.


Valuable explanation on the entropy , as i never saw before !