Internal Controls for Bitcoin Custody
Bitcoin custody requires strict safeguards to prevent loss or theft. Unlike traditional financial systems, Bitcoin transactions are irreversible, making robust security measures essential. Internal controls focus on:
- Access Management: Use multi-signature wallets to prevent single points of failure.
- Key Security: Distribute private keys across locations and individuals.
- Real-Time Monitoring: Spot unusual activity instantly.
- Backup & Recovery: Ensure funds can be accessed during emergencies.
Institutions must also address challenges like scaling operations, managing technical complexities, and adapting to new threats. Tools like Miniscript and threshold signatures offer advanced security options. Regular audits, compliance checks, and disaster recovery drills further strengthen defenses.
Key Takeaway: A layered approach combining technology, processes, and human oversight ensures Bitcoin assets remain secure.
How Top Institutions Manage Risk, Custody & Compliance in Crypto | UK & Global Perspectives
Core Components of an Internal Control Framework
When it comes to safeguarding institutional Bitcoin holdings, a strong internal control framework is non-negotiable. The irreversible nature of Bitcoin transactions demands rigorous preventive measures to ensure the security of funds.
Access Controls and Multi-Signature Wallets
One of the cornerstones of this framework is implementing strict access controls, with multi-signature (multisig) wallets playing a central role. These wallets require multiple private keys to approve a transaction, significantly reducing the risk of a single point of failure – a crucial factor for institutional Bitcoin custody.
Emerging technologies like Miniscript and threshold signatures take security a step further. They allow for more adaptable policies and distribute signing authority across multiple parties, adding an extra layer of protection.
Best Practices for Securing Bitcoin Using Multisig Wallets
Securing Bitcoin with multisig wallets involves more than just setting up the technology – it requires thoughtful planning and adherence to proven strategies that ensure both safety and efficiency.
Understanding Multisig Wallet Structures
Multisig wallets rely on specific configurations to manage access controls effectively. For example, a 2-of-3 setup requires any two out of three keys to authorize a transaction. This strikes a balance between security and ease of use.
For institutions handling larger sums, a 3-of-5 configuration offers an extra layer of security. With this setup, three signatures are needed out of five possible keys. This allows for redundancy and supports more complex governance, where keys can be distributed across departments or even different locations.
Another advanced option is threshold signatures, which streamline the process by producing a single signature that confirms the required number of participants. This reduces transaction size and improves privacy.
There’s also Miniscript, which allows for more flexible spending conditions within a multisig setup. For instance, it can enable emergency procedures or implement time-based access rules, adding another layer of customization.
Steps to Securely Set Up and Manage Multisig Wallets
Once you understand how multisig configurations work, the next step is to ensure they’re deployed securely. Here’s how:
- Generate Keys Safely: Always create private keys on air-gapped devices to keep them offline. Avoid generating multiple keys on the same device or in the same location to reduce risk.
- Distribute Keys Strategically: Store keys in separate physical locations, ideally across different time zones, and assign them to different individuals or departments. This minimizes the chance of a single event compromising multiple keys.
- Validate Keys Regularly: Conduct quarterly tests to ensure all keys are accessible without signing any transactions. Keep secure records of these validations as part of your protocol.
- Use Hardware Wallets: Hardware wallets help isolate private keys from online threats. Choose wallets compatible with your multisig setup and purchase them directly from the manufacturer to avoid supply chain risks.
- Implement Verification Protocols: Require multiple parties to independently confirm transaction details, such as recipient addresses and amounts, before signing. This extra step can catch errors and guard against social engineering attacks.
These practices align with institutional internal controls, creating a strong foundation for secure Bitcoin custody.
Using BitVault for Institutional Custody
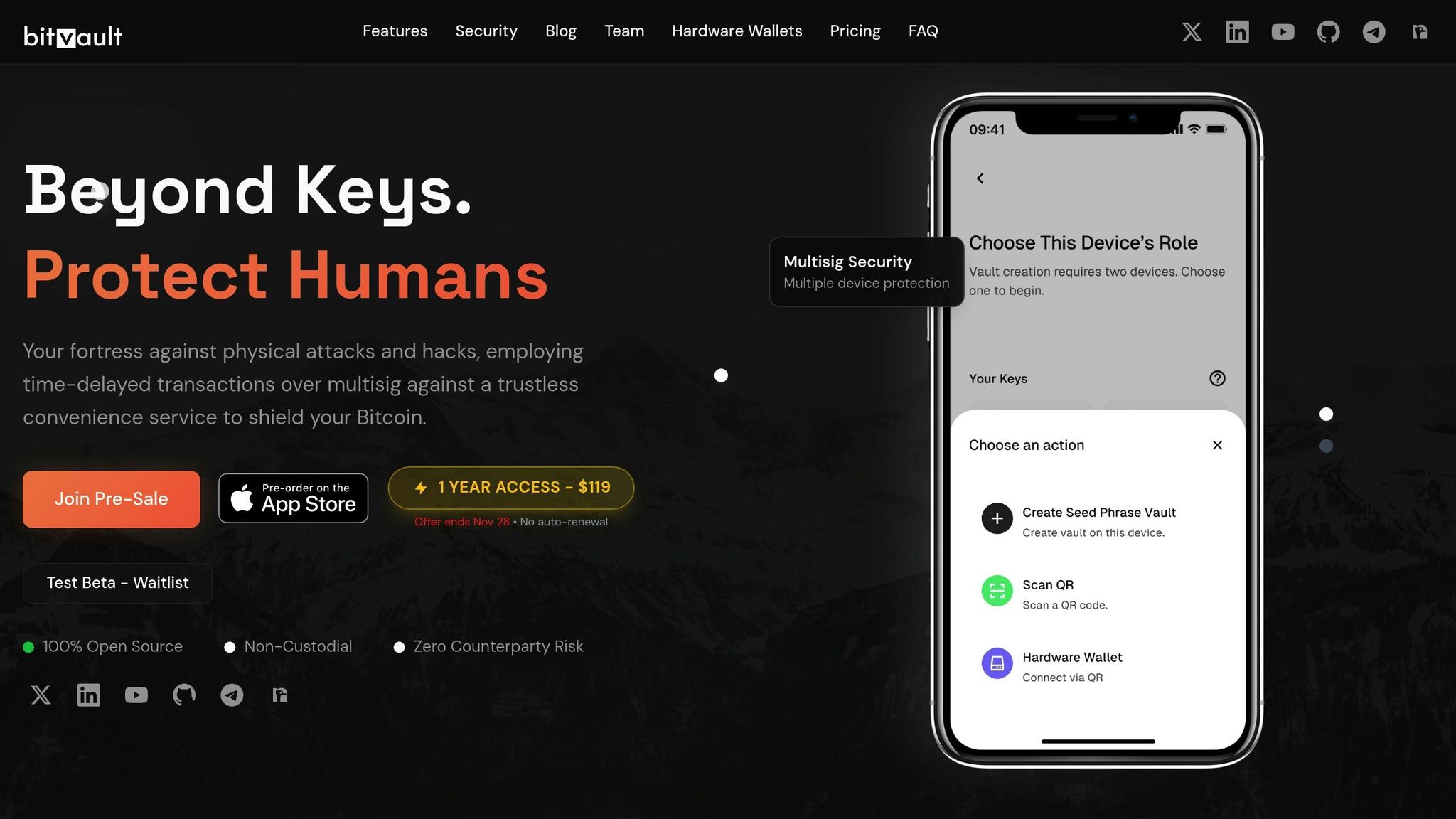
For institutions, BitVault offers a robust solution to enhance Bitcoin security. Its suite of features addresses common custody challenges while integrating seamlessly with existing systems.
One standout feature is time-delayed transactions, which introduce a mandatory waiting period before transfers are finalized. This delay provides a critical window to detect and cancel unauthorized transactions, protecting against both physical coercion and sophisticated digital attacks.
Another key feature is secret notifications, which send encrypted alerts to designated devices whenever a transaction is attempted. These alerts function independently of primary communication channels, ensuring that security teams are informed even if other systems are compromised.
BitVault also supports hardware wallets like Jade Plus, alongside other trusted devices. This compatibility allows institutions to maintain their current infrastructure while benefiting from BitVault’s added security, reducing the complexity of implementation and training.
The platform’s open-source architecture builds trust by allowing security teams to audit the codebase and verify its claims. Additionally, BitVault simplifies the technical aspects of multisig coordination, enabling institutions to focus on governance and decision-making rather than grappling with technical hurdles.
For organizations managing long-term Bitcoin holdings or generational wealth, BitVault’s combination of time delays, multisig requirements, and secret notifications offers a security framework that is both resilient and adaptable to evolving threats.
sbb-itb-7e890ce
Auditing, Monitoring, and Compliance for Bitcoin Custody
When it comes to institutional Bitcoin custody, having robust systems for auditing, monitoring, and compliance isn’t just a good idea – it’s a necessity. These processes protect digital assets, ensure adherence to regulatory requirements, and build trust with stakeholders.
Routine Reconciliation and Addressing Discrepancies
Daily reconciliation serves as the backbone of Bitcoin custody. This process compares on-chain transactions with internal records to identify and address any discrepancies. It starts with verifying Bitcoin addresses against a master list. If any unexpected changes are detected, they’re flagged for immediate investigation. Key transaction details – such as amounts, timestamps, and recipient addresses – are then cross-checked against authorized logs. Any irregularities are meticulously documented, including when they were discovered, the steps taken to investigate, and how they were resolved.
While automated tools are invaluable for continuously scanning blockchain data and spotting irregular patterns, human oversight remains critical to ensure nothing slips through the cracks.
These reconciliation practices are vital for both internal reviews and external audit processes.
The Importance of Internal and External Audits
Audits play a key role in ensuring the integrity of Bitcoin custody. External audits, conducted periodically, validate custody practices without compromising private keys. Meanwhile, internal audits focus on reviewing access logs, approval workflows in multisignature setups, and emergency protocols. They also assess whether roles and responsibilities are properly segregated, ensuring no single individual has unchecked authority to approve transactions.
Clear and organized documentation is essential to back up audit findings and demonstrate compliance.
Real-Time Monitoring to Spot Anomalies
Real-time monitoring builds on audit insights to detect irregularities as they happen. These systems are designed to guard against unauthorized activity by analyzing transaction patterns, amounts, and timing. By establishing a baseline of normal behavior, monitoring tools can quickly identify deviations that may signal a potential threat.
Monitoring isn’t limited to institutional wallets. For example, if Bitcoin is transferred to addresses linked to exchanges or mixing services without proper authorization, these transactions are flagged for review. Additional layers of analysis – such as evaluating transactions based on time and location – ensure that unusual activity, like transfers occurring at odd hours or from unexpected regions, gets immediate attention.
Multi-tiered alerts notify security teams right away, enabling quick responses. When integrated with existing security systems, these monitoring solutions provide a complete picture of potential threats, ensuring institutions can act swiftly to mitigate risks.
Backup, Recovery, and Continuity Planning for Bitcoin Custody
When it comes to Bitcoin custody, mistakes can be costly – often irreversibly so. A lost private key means lost funds, with no way to recover them. That’s why having a solid backup, recovery, and continuity strategy is not optional; it’s essential. Below, we’ll explore practical steps to safeguard institutional Bitcoin assets and ensure operations remain resilient.
Designing Secure Backup and Recovery Processes
Creating a reliable backup system for Bitcoin custody requires a careful balance between security and accessibility. One of the key principles is diversification: store backups in multiple secure locations, ideally spread across different geographic regions.
For multisignature (multisig) setups, it’s critical to treat each key component separately. This means backing up seed phrases, hardware wallet recovery details, and wallet configuration files independently – and storing them in different secure locations. Keeping all these elements in one place undermines the entire purpose of a multisig system.
When dealing with hardware wallets, don’t just stop at the seed phrase. Include firmware versions, wallet configurations, and any specific settings in your backup plan. A standardized checklist can help ensure nothing important is missed during the process.
Documentation is another cornerstone of a strong recovery plan. Record wallet structures, threshold requirements for multisig wallets, key holder roles, and emergency contact details. Testing these backups in non-production environments on a regular basis is equally important, as it helps identify vulnerabilities before they become critical.
Periodic Key Validation and Inheritance Planning
Regularly validating keys is a must. By performing test signatures periodically, institutions can ensure that their backups remain functional and ready for use. This is especially crucial for high-value Bitcoin custody operations, where any failure could lead to significant financial loss.
Inheritance planning for institutional Bitcoin holdings is more complex than personal arrangements. It involves navigating regulatory compliance, obtaining board approvals, and adhering to governance protocols. A well-crafted plan should clearly outline how funds can be accessed if primary key holders are unavailable. This includes emergency contacts, legal authorizations, and technical steps for wallet reconstruction. To add an extra layer of protection, institutions can implement time-locked transactions, which delay fund access and provide a buffer against unauthorized use.
These processes should integrate seamlessly with existing auditing and access control measures to ensure consistency.
Disaster Recovery and Business Continuity
Disaster recovery planning is essential for maintaining operations during crises. Whether it’s a key compromise, hardware failure, or a disruption to facilities, a strong recovery plan ensures that institutions can act quickly and effectively.
In the case of a compromised key, the plan should detail how remaining valid keys can be used to move funds to secure addresses, notify stakeholders, and conduct forensic investigations to determine the cause of the breach. For hardware failures, having spare devices pre-configured and ready to deploy can minimize downtime.
Geographic diversification is another critical element. Distributed key holders, redundant communication channels, and alternative facilities can all help maintain operational resilience. Preconfigured emergency wallets are also useful for speeding up response times in urgent situations.
Clear communication is vital during a crisis. Establish secure channels, identify emergency contacts, and define escalation procedures in advance. Business continuity planning should also account for regulatory requirements, with pre-drafted reporting templates and clear guidelines for incident reporting.
Advanced security tools, like BitVault’s time-delayed transaction system, can add another layer of protection. These systems enforce mandatory waiting periods, giving institutions time to detect and respond to unauthorized activity before funds are moved.
Finally, regular disaster recovery drills are indispensable. Simulating various failure scenarios allows institutions to refine their plans, improve communication, and strengthen overall resilience. The lessons learned from these exercises can make all the difference when it matters most.
Conclusion and Key Takeaways
Summary of Core Recommendations
Building strong internal controls requires a layered strategy that integrates technology, well-defined processes, and human oversight. One standout solution is the use of multisig wallets, which spread control among multiple parties, reducing the risk of a single point of failure. When paired with time-based mechanisms that introduce delays to transactions, these wallets gain an added layer of protection, offering critical moments to detect and stop unauthorized actions.
Tools like Miniscript allow for highly tailored multisig policies, giving institutions the flexibility to meet unique security needs. Additionally, self-custody eliminates the vulnerabilities tied to storing assets on centralized exchanges. Features like time-locked contracts not only bolster security but can also streamline operations, making them a key element in forward-thinking risk management strategies.
Final Thoughts on Institutional Bitcoin Security
These recommendations form the foundation for advancing Bitcoin security practices. As the landscape evolves, the continuous development of multisig wallet technologies is becoming a standard. Regularly assessing and adopting cutting-edge security tools is crucial to address new and emerging threats. By incorporating multisig, time-delay mechanisms, and advanced protocols, institutions can better navigate Bitcoin’s irreversible transaction framework, ensuring their assets are protected in an increasingly complex digital environment.
FAQs
What are the benefits of using multisig wallets over single-signature wallets for Bitcoin custody?
Multisig wallets add an extra layer of security by requiring multiple private keys to approve any transaction. This means funds can’t be moved by just one person, significantly lowering the risk of theft or accidental loss.
For institutions, these wallets provide a practical way to share control among several parties, establishing stronger internal checks and balances. Whether you’re protecting Bitcoin on a personal level or managing it within an organization, multisig wallets are a smart solution for keeping assets secure.
How do tools like Miniscript and threshold signatures improve Bitcoin transaction security?
Threshold signatures take Bitcoin security to the next level by splitting a private key into several parts, so no single entity has complete control. This method not only minimizes the risk of a key being compromised but also keeps transactions looking like regular single-signature ones on the blockchain. The result? Better privacy and lower transaction costs.
Miniscript complements this by streamlining complex Bitcoin scripts. It simplifies the process of setting up and reviewing spending conditions, making it easier to ensure everything is secure. When combined, these tools offer strong safeguards against potential threats, enabling safer and more efficient Bitcoin transactions.
What should institutions consider when creating a disaster recovery plan for Bitcoin custody?
When creating a disaster recovery plan for Bitcoin custody, institutions need to prioritize security, redundancy, and accessibility. A good starting point is using multi-signature wallets, which prevent a single point of failure from jeopardizing funds. Additionally, wallet data should be backed up regularly and stored securely across multiple locations to reduce risks tied to geographic limitations.
Equally important is establishing clear recovery procedures. This includes assigning specific roles and responsibilities to team members to streamline the recovery process in case of an incident. Regularly testing the recovery plan is essential to uncover and fix any vulnerabilities before they become critical issues. Lastly, ensure the plan aligns with relevant regulations and industry standards to safeguard assets and maintain smooth operations.
Related Blog Posts
- Bitcoin Wallet Backup: Complete Security Checklist
- Never leave Bitcoin on Exchanges, Learnings from Bitcoin7.com Hack in 2011
- Bitcoin Treasury Compliance vs. Risk
- Multisig Wallets: Reducing Mnemonic Risks
https://app.seobotai.com/banner/banner.js?id=691bd32260ed14ccdc7ec480